Consulting Engagement
Objective Cybersecurity Risk Assessments
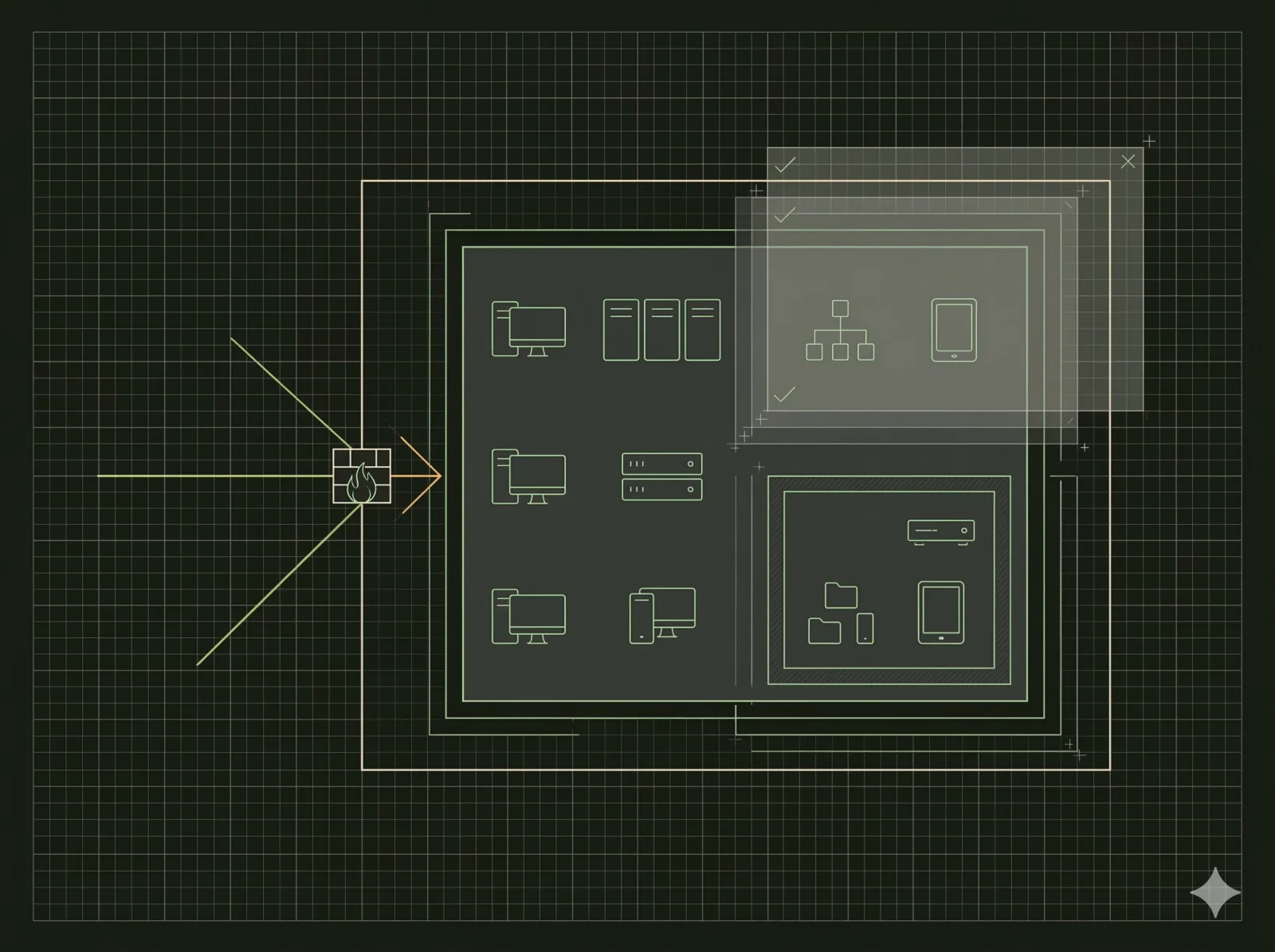
Many businesses falsely assume their current IT provider has secured every vulnerable endpoint. Unfortunately, network perimeters often degrade over time as new software gets installed, employees change roles, and firewall firmware ages. Valet Cyber provides independent, project-based cybersecurity assessments for organizations operating in New York and the surrounding states. We act as an impartial third party to audit your digital environment. Our goal is strictly analytical: we find the hidden gaps in your armor and provide a clear roadmap to seal them, completely free of high-pressure managed service pitches.
Comprehensive Vulnerability Scanning
Our security consultants deploy enterprise-grade diagnostic tools to probe your network both from the outside internet and from within your physical office. We simulate the tactics used by modern ransomware operators to identify unpatched software, open server ports, and misconfigured cloud storage buckets. We also review your Microsoft 365 or Google Workspace tenant for critical administrative oversights, such as disabled multi-factor authentication or overly permissive email forwarding rules.
- Perimeter Testing: We analyze your edge firewalls for exploitable firmware bugs and outdated access policies.
- Identity Auditing: We check for compromised employee passwords cross-referenced against global data breach databases.
- Phishing Simulation: We evaluate employee security awareness through controlled, safe email testing.
- Data Flow Analysis: We map where your sensitive financial and client information lives and who holds access to it.
Actionable Remediation Guidelines
We translate complex technical vulnerabilities into plain English business risks. At the conclusion of our engagement, you receive a comprehensive Executive Summary alongside a highly detailed technical appendix. We prioritize all discovered vulnerabilities by severity, categorizing them into critical fixes, moderate improvements, and long-term strategic goals. You can hand this final report directly to your internal IT director or existing vendor to execute the repairs. Our documentation provides the exact proof you need to satisfy board members, cyber insurance underwriters, or demanding enterprise clients.